In his quest to turn a simple and functioning Twitter app into X, the everything app that doesn’t do anything very well, Elon Musk launched audio and video calling on X last week — and this new feature is switched on by default, it leaks your IP address to anyone you talk with, and it’s incredibly confusing to figure out how to limit who can call you.
In a post on Wednesday, X’s official news account announced the new feature: “audio and video calling are now available to everyone on X! who are you calling first?” X wrote.
We looked at X’s official help center page and ran tests of the feature to analyze how the calling feature works and to understand the risks associated with it.
A person’s IP address is not hugely sensitive, but these online identifiers can be used to infer location and can be linked to a person’s online activity, which can be dangerous for high-risk users.
First of all, the audio and video calling feature is inside the Messages part of the X app, where a phone icon now appears in the top right-hand corner, both on iOS and Android.
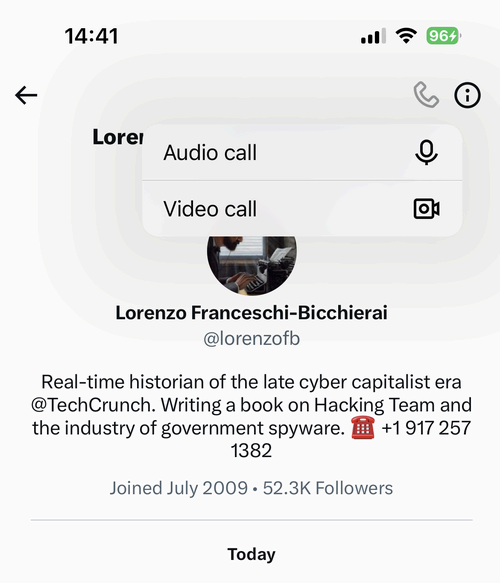
A screenshot of X’s audio and video calling feature on iOS. Image Credits: TechCrunch
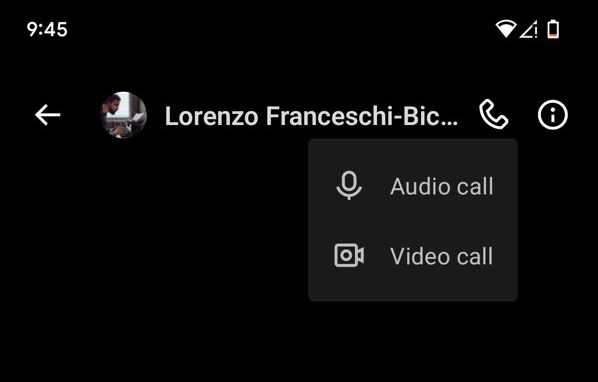
A screenshot of X’s audio and video calling feature on Android. Image Credits: TechCrunch
Calling is enabled by default in the X apps. The caveat is that you can only make and receive calls on X’s app, and not yet in your browser.
By default, calls are peer-to-peer, which means that the two people in a call share each others’ IP addresses because the call connects to their devices directly. This happens by design in most messaging and calling apps, such as FaceTime, Facebook Messenger, Telegram, Signal, and WhatsApp, as we reported in November.
In its official help center, X says that calls are routed peer-to-peer between users in a way that IP addresses “may be visible to the other.”
If you want to hide your IP address, you can turn on the toggle “Enhanced call privacy” in X’s Message settings. By switching on this setting, X says the call “will be relayed through X infrastructure, and the IP address of any party that has this setting enabled will be masked.”
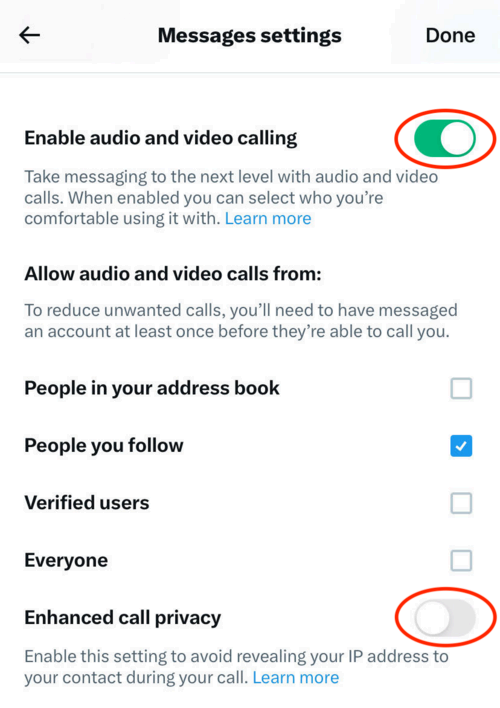
A screenshot of the settings for X’s audio and video calling feature for iOS. Image Credits: TechCrunch
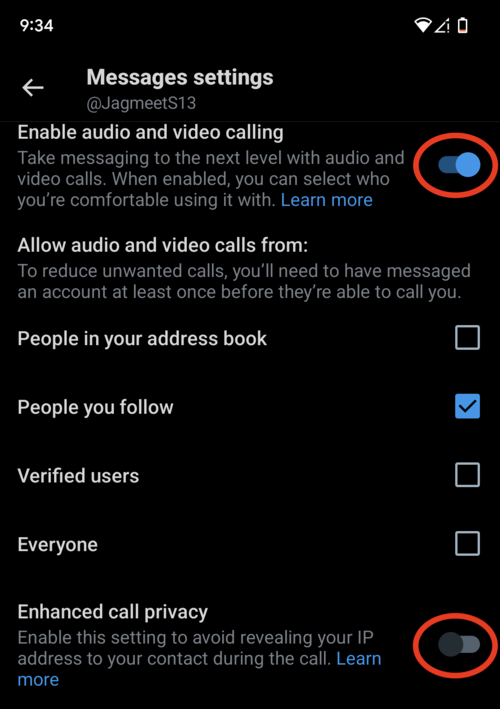
A screenshot of the settings for X’s audio and video calling feature for Android. Image Credits: TechCrunch
X doesn’t mention encryption in the official help center page at all, so the calls are probably not end-to-end encrypted, potentially allowing Twitter to listen in on conversations. End-to-end encrypted apps, Signal or WhatsApp — prevent anyone other than the caller and the recipient from listening in, including WhatsApp and Signal.
We asked X’s press email whether there is end-to-end encryption. The only response we got was: “Busy now, please check back later,” X’s default auto-response to media inquiries. We also emailed X spokesperson Joe Benarroch but did not hear back.
Because of these privacy risks, we recommend switching off the calling feature completely.
In case you do want to use this call feature, it’s important to understand who can call you and who you can call — and depending on your settings, it can get very confusing and complicated.
The default setting (as you can see above) is “People you follow,” but you can choose to change it to “People in your address book,” if you shared your contacts with X; “Verified users,” which would allow anyone who pays for X to call you; or everyone, if you would like to receive spam calls from any rando.
TechCrunch decided to test several different scenarios with two X accounts: a newly created test account and a long-standing real account. Using open source network analysis tool Burp Suite, we could see the network traffic flowing in and out of the X app.
Here are the results (at the time of writing):
- When neither account follows each other, neither account sees the phone icon, and thus neither can call.
- When the test account sends a DM to the real account, the message is received but neither account sees the phone icon.
- When the real account accepts the DM, the test account can then call the real account. And if nobody picks up, only the test account caller’s IP is exposed.
- When the test account starts a call and the real account picks up (which exposes the real account’s IP address — so both sets of IP addresses), the test account cannot call back because the test account is set to allow incoming calls for “follow” only.
- When the real account follows the test account back, both can contact each other.
The network analysis shows that X built the calling feature using Periscope, Twitter’s livestreaming service and app that was discontinued in 2021. Because X’s calling uses Periscope, our network analysis shows the X app creates the call as if it were a live Twitter/X broadcast, even if the contents of the call cannot be heard.
Ultimately, whether to use X calling is your choice. You can do nothing, which potentially exposes you to calls from people you probably don’t want to get calls from and can compromise your privacy. Or you can try to limit who can call you by deciphering X’s settings. Or, you can just switch off the feature altogether and not have to worry about any of this.
Carly Page and Jagmeet Singh contributed reporting.

