
This was a bad week for ransomware, with the Trigona ransomware suffering a data breach and law enforcement disrupting the RagnarLocker ransomware operation.
Last week, Ukrainian hacktivists known as the Ukrainian Cyber Alliance hacked the Trigona gang’s servers by exploiting a vulnerability in their Confluence server.
This ultimately allowed the activists to breach other sites run by Trigona to take data, copies of internal chats, and the website source code. They then wiped Trigona’s Tor negotiation and data leak sites, defacing them with the message below.
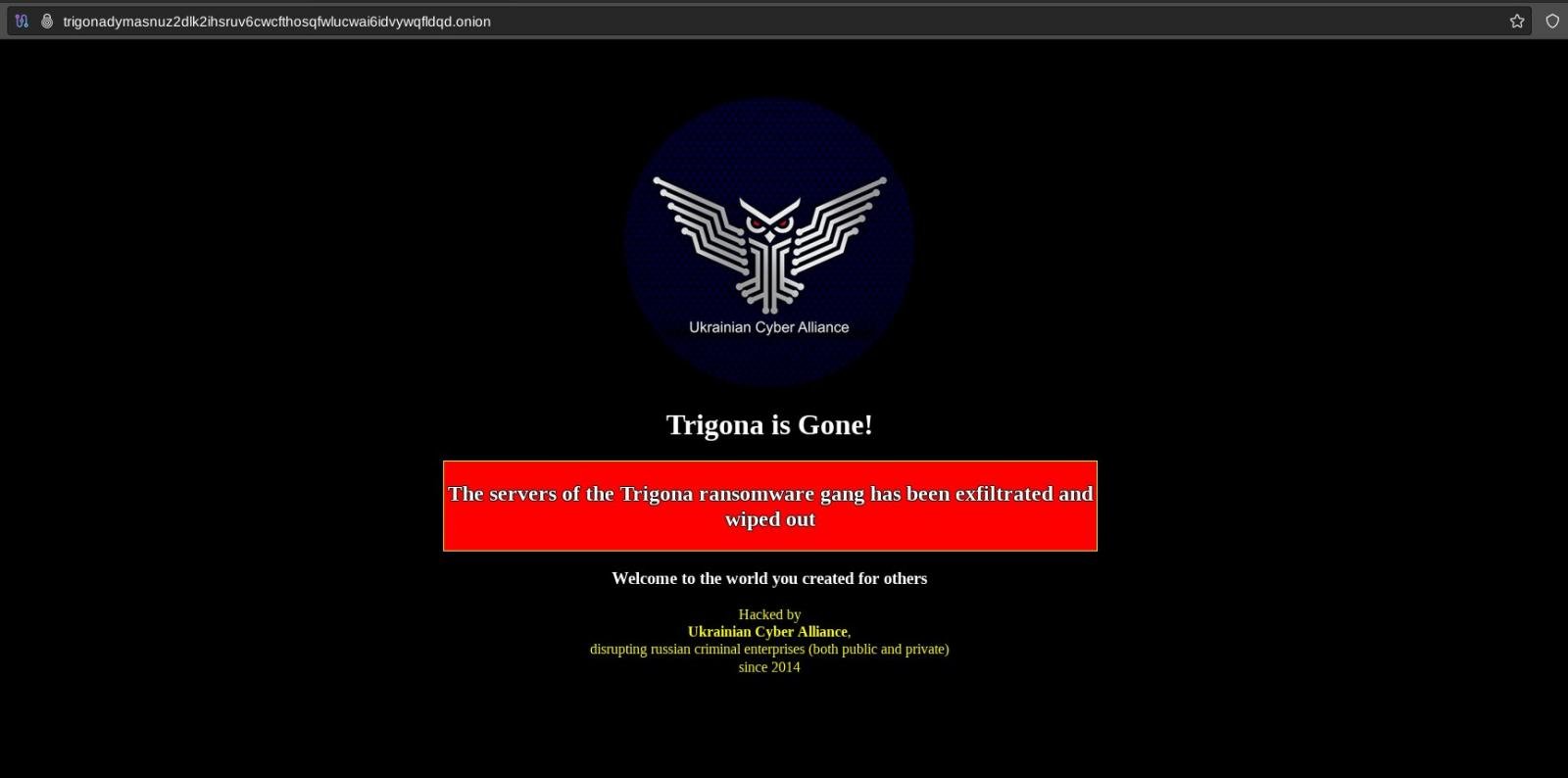
Source: BleepingComputer
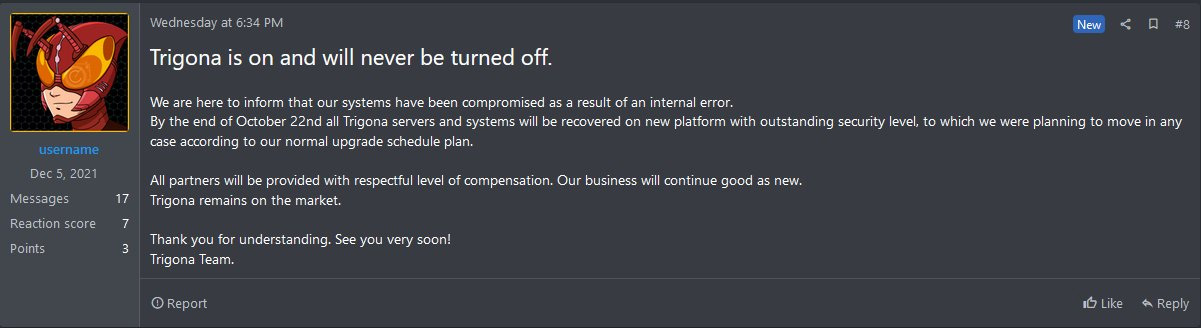
Trigona later admitted they were breached and said they plan on launching new sites on October 22nd.
On Thursday, the RagnarLocker data leak site and negotiation site also began to show a new message, this time a seizure banner by law enforcement from France, the Czech Republic, Germany, Italy, Latvia, the Netherlands, Spain, Sweden, Japan, Canada, and the United States.
As part of this international law enforcement operation, police arrested a malware developer linked with the RagnarLocker ransomware gang and seized the group’s dark websites
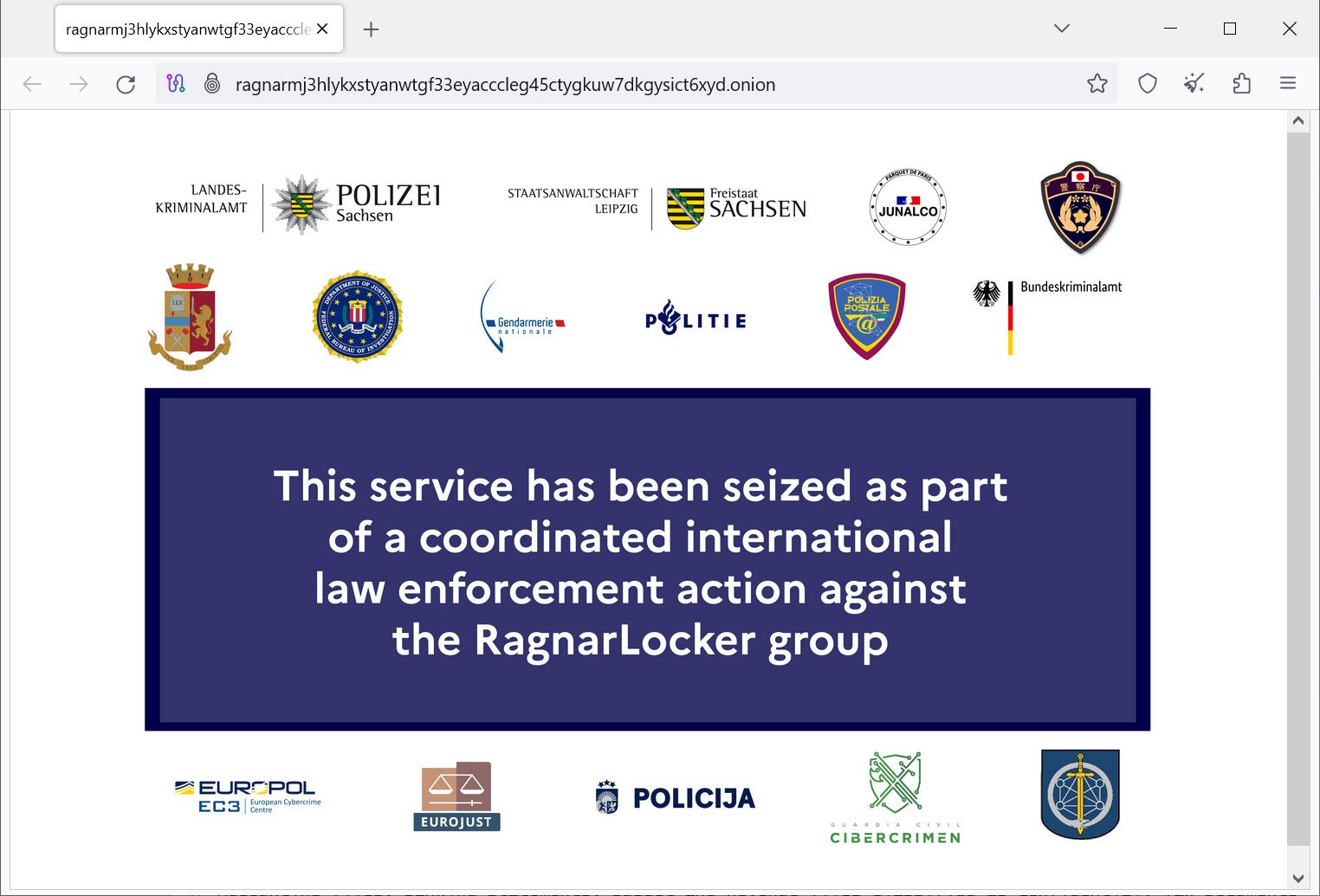
Source: BleepingComputer
This is a significant action as RagnarLocker is one of the oldest, still-active ransomware operations, having conducted attacks against 168 international companies globally since 2020
In other news, we learned more about cyberattacks against various companies, with a BlackBasta attack against TV advertising firm Ampersand and Kwik Trip finally confirming they suffered a cyberattack, though it was not confirmed to be ransomware.
Finally, cybersecurity researchers released interesting reports on ransomware, including:
Contributors and those who provided new ransomware information and stories this week include: @LawrenceAbrams, @serghei, @fwosar, @Ionut_Ilascu, @billtoulas, @Seifreed, @demonslay335, @malwrhunterteam, @BleepinComputer, @vx_herm1t, @AlvieriD, @AShukuhi, @pcrisk, @rivitna2, @BushidoToken, @ResilienceSays, @SophosXOps, @Unit42_Intel, @jgreigj, @azalsecurity, @AShukuhi, @Cynet360, @FalconFeedsio, and @cyber_int.
October 15th 2023
Colonial Pipeline attributes ransomware claims to ‘unrelated’ third-party data breach
Colonial Pipeline said there has been no disruption to pipeline operations or their systems after a ransomware gang made several threats on Friday afternoon.
October 16th 2023
New STOP ransomware variants
PCrisk found new STOP ransomware variants that append the .ptqw and .pthh extensions.
New MedusaLocker variant
PCrisk found a new MedusaLocker variant that appends the .crypto1317 extension and drops a ransom note named How_to_back_files.html.
New Chaos variant
PCrisk found a new Chaos variant that appends the .MesaCorp extension and drops a ransom note named read_it.txt.
October 17th 2023
KwikTrip all but says IT outage was caused by a cyberattack
Kwik Trip has released another statement on an ongoing outage, all but confirming it suffered a cyberattack that has led to IT system disruptions.
TV advertising sales giant affected by ransomware attack
A television advertising sales and technology company jointly owned by the three largest U.S. cable operators was hit with a ransomware attack in recent weeks that affected operations.
New Dharma variant
PCrisk found a new Dharma ransomware variant that appends the .2023 extension.
New STOP variant
PCrisk found a new Dharma ransomware variant that appends the .ptrz extension.
New EarthGrass ransomware
PCrisk found a new ransomware named EarthGrass that appends the .34r7hGr455 extnesion and drops a ransom note named Read ME (Decryptor).txt.
New KeyLock ransomware
PCRisk found the new KeyLocker ransomware that appends the .keylock extension and drops a ransom note named README-id-[username].txt.
October 18th 2023
Ukrainian activists hack Trigona ransomware gang, wipe servers
A group of cyber activists under the Ukrainian Cyber Alliance (UCA) banner has hacked the servers of the Trigona ransomware gang and wiped them clean after copying all the information available.
Resilience 2023 Claims Report
The first half of 2023 has once again seen an upheaval in the cybercrime industry. From Russian firms potentially licensing out advanced malware to affiliate partners in the US and UK, to attacks against relatively unknown third-party SaaS suppliers scaling to thousands of victim organizations at once, cybercrime actors are once again adeptly reacting to a shift in their market. As companies become more resistant to paying extortions, Resilience is seeing a move towards going after bigger fish and swimming upstream to hit vendors and bypass security controls. This has significant implications for those defending their organizations and trying to limit financial losses from these actors.
GhostLocker: The New Ransomware On The Block
Over the past week, an establishment of a new ransomware franchise has emerged named GhostLocker. Ghost Locker is a new Ransomware-as-a-Service (Raas) established by several hacktivist groups led by GhostSec.
Pro-Palestinian hacktivisits claim to use Crucio ransomware
A new pro-Palestinian hacktivist group called Soldiers Of Solomon claim to be deploying a new Crucio Ransomware.
October 19th 2023
Ragnar Locker ransomware’s dark web extortion sites seized by police
The Ragnar Locker ransomware operation’s Tor negotiation and data leak sites were seized Thursday morning as part of an international law enforcement operation.
BlackCat ransomware uses new ‘Munchkin’ Linux VM in stealthy attacks
The BlackCat/ALPHV ransomware operation has begun to use a new tool named ‘Munchkin’ that utilizes virtual machines to deploy encryptors on network devices stealthily.
Ransomware actor exploits unsupported ColdFusion servers—but comes away empty-handed
In September and early October, we saw several efforts by a previously unknown actor to leverage vulnerabilities in obsolete, unsupported versions of Adobe’s ColdFusion Server software to gain access to the Windows servers they ran on and pivot to deploying ransomware. None of these attacks were successful, but they provided telemetry that allowed us to associate them with a single actor or group of actors, and to retrieve the payloads they attempted to deploy.
Megazord ransomware analysis
A new version of the Akira ransomware called “Megazord” emerged around August 2023. It changes the names of your files by adding “.Powerrangers” at the end. Several static and code similarities suggest that Megazord could be an attempt to give Akira a new look. Such alteration might be an attempt to rebrand the Akira ransomware since it has become familiar to widespread recognition throughout the cybersecurity community.
Trigona’s responds to their takedown by UCA
As seen by AzAl Security, the Trigona ransomware operation has responded to UCA’s takedown of their sites, claiming to return on the 22nd.
October 20th 2023
Kwik Trip finally confirms cyberattack was behind ongoing outage
Two weeks into an ongoing IT outage, Kwik Trip finally confirmed that it’s investigating a cyberattack impacting the convenience store chain’s internal network since October 9.
Ragnar Locker ransomware developer arrested in France
Law enforcement agencies arrested a malware developer linked with the Ragnar Locker ransomware gang and seized the group’s dark web sites in a joint international operation.
New STOP ransomware variants
PCrisk found new STOP ransomware variants that append the .ithh, .itqw, and .itrz extensions.
New Hunters International uses Hive encryptor
rivitna discovered the new Hunters International ransomware, which appears to be using an encryptor from the Hive operation.

