
A threat actor is using an open-source network mapping tool named SSH-Snake to look for private keys undetected and move laterally on the victim infrastructure.
SSH-Snake was discovered by the Sysdig Threat Research Team (TRT), who describe it as a “self-modifying worm” that stands out from traditional SSH worms by avoiding the patterns typically associated with scripted attacks.
The worm searches for private keys in various locations, including shell history files, and uses them to stealthily spread to new systems after mapping the network.
SSH-Snake is available as an open-source asset for automated SSH-based network traversal, which can start from one system and show the relationship with other hosts connected through SSH.
However, researchers at Sysdig, a cloud security company, say that SSH-Snake takes the typical lateral movement concept to a new level because it is more rigorous in its search for private keys.
Released on January 4, 2024, SSH-Snake is a bash shell script tasked with autonomously searching a breached system for SSH credentials and utilizing them for propagation.
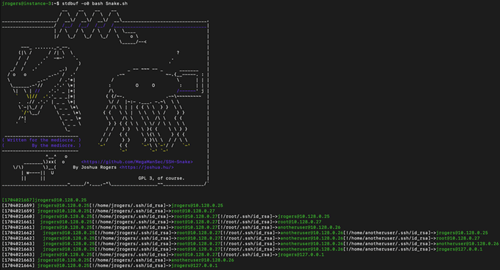
The researchers say that one particularity of SSH-Snake is the ability to modify itself and make itself smaller when running for the first time. It does this by removing comments, unnecessary functions, and whitespace from its code.
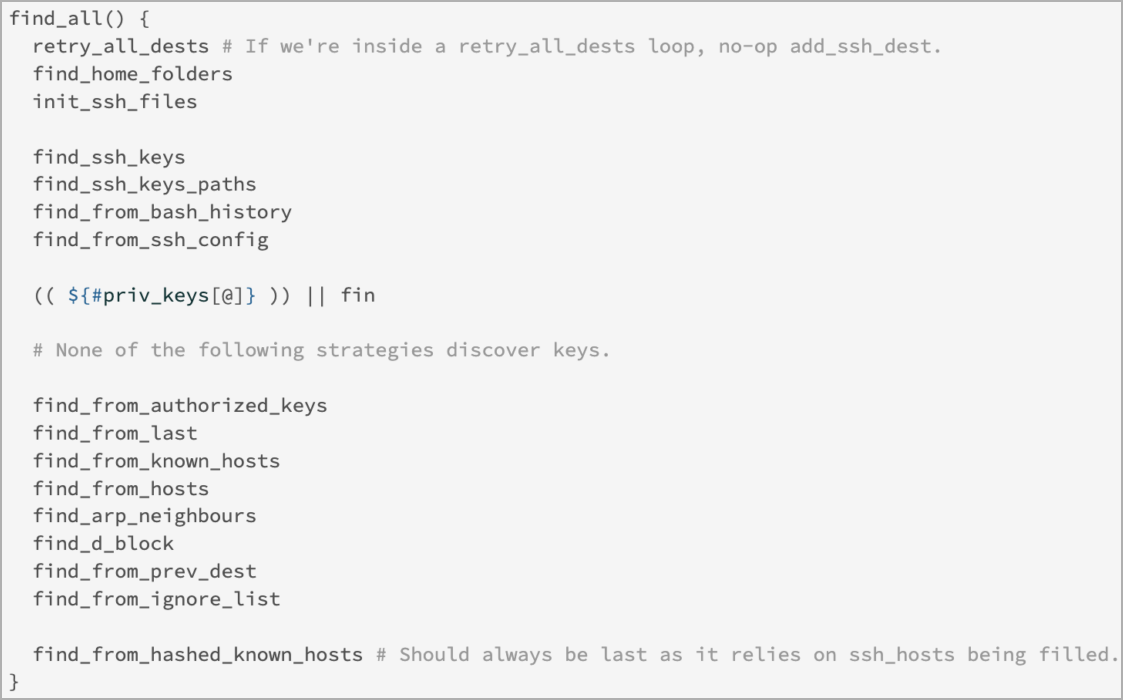
Designed for versatility, SSH-Snake is plug-and-play yet allows customizing for specific operational needs, including adapting strategies to discover private keys and identify their potential use.
SSH-Snake employs various direct and indirect methods to discover private keys on compromised systems, including:
- Searching through common directories and files where SSH keys and credentials are typically stored, including .ssh directories, config files, and other locations.
- Examining shell history files (e.g., .bash_history, .zsh_history) to find commands (ssh, scp, and rsync) that may have used or referenced SSH private keys.
- Using the ‘find_from_bash_history’ feature to parse the bash history for commands related to SSH, SCP, and Rsync operations, which can uncover direct references to private keys, their locations, and associated credentials.
- Examining system logs and network cache (ARP tables) to identify potential targets and gather information that might indirectly lead to discovering private keys and where they can be used.
Sysdig’s analysts confirmed SSH-Snake’s operational status after discovering a command and control (C2) server used by its operators to store data harvested by the worm, including credentials and victim IP addresses.
This data shows signs of active exploitation of known Confluence vulnerabilities (and possibly other flaws) for initial access, leading to the deployment of the worm on these endpoints.
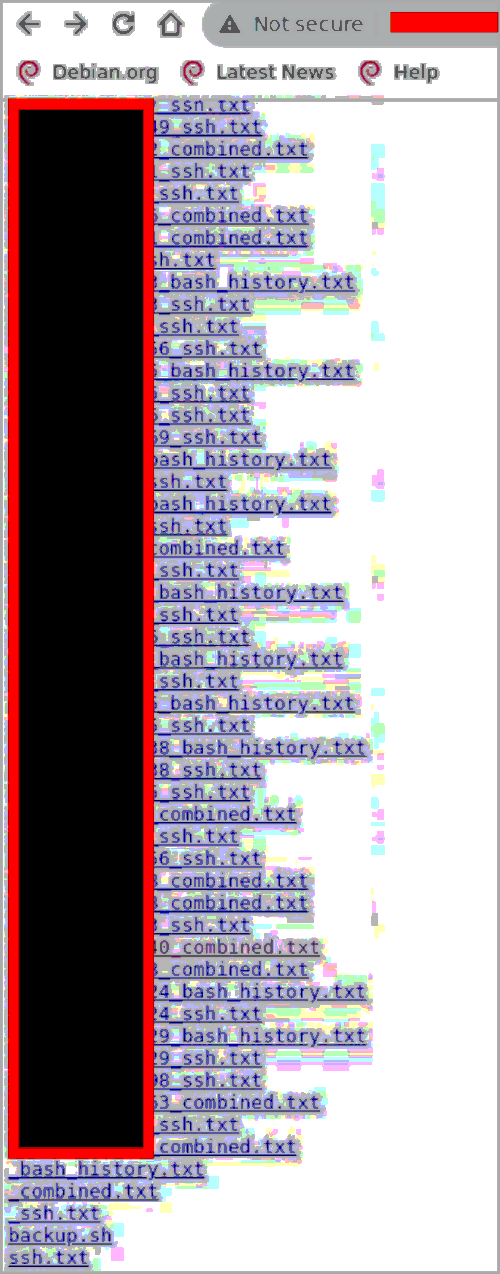
(Sysdig)
According to the researchers, the tool has been used offensively on around 100 victims.
Sysdig sees SSH-Snake as “an evolutionary step” as far as malware goes because it targets a secure connection method that is widely used in corporate environments.

