If an iPhone has already been infected with malware, Jamf has shown how an attacker can trick the user into believing Lockdown Mode is active when it isn’t.
Despite popular belief, iPhones can get infected with malware — but it is rare. Attackers taking advantage of zero-day vulnerabilities and zero-click exploits can infect a user’s device — though these sophisticated attacks are often expensive and difficult to execute.
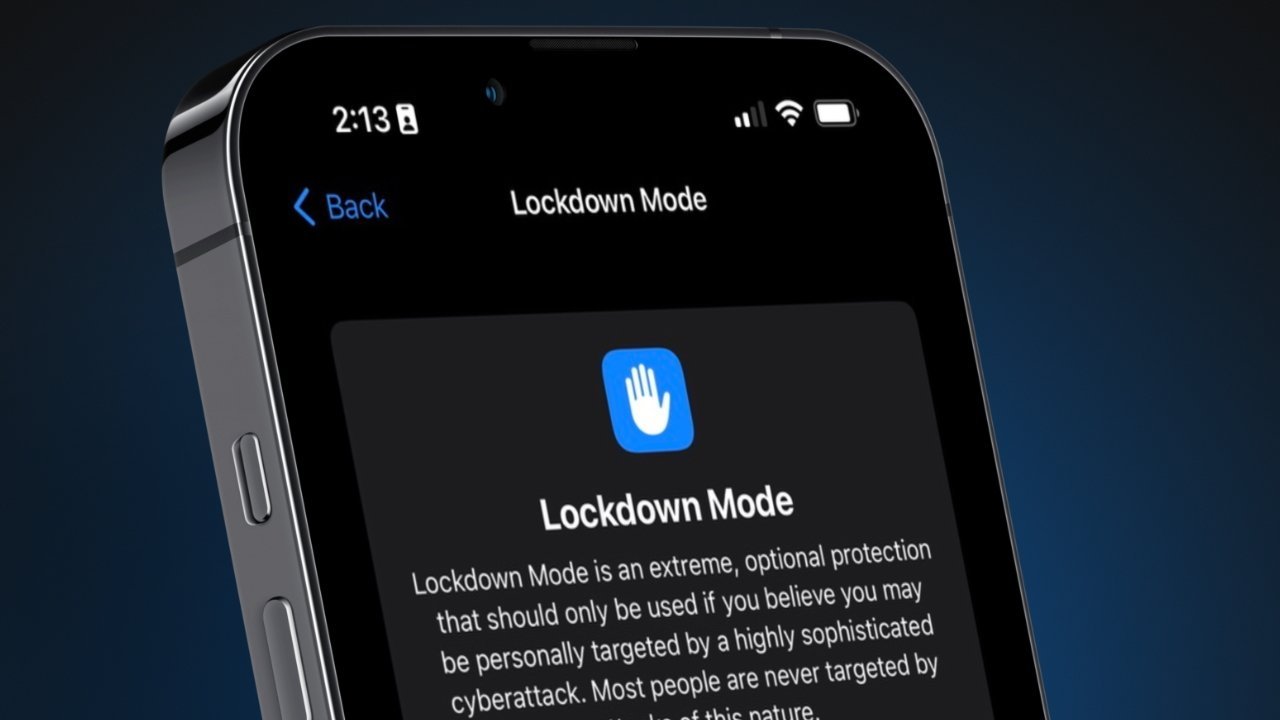
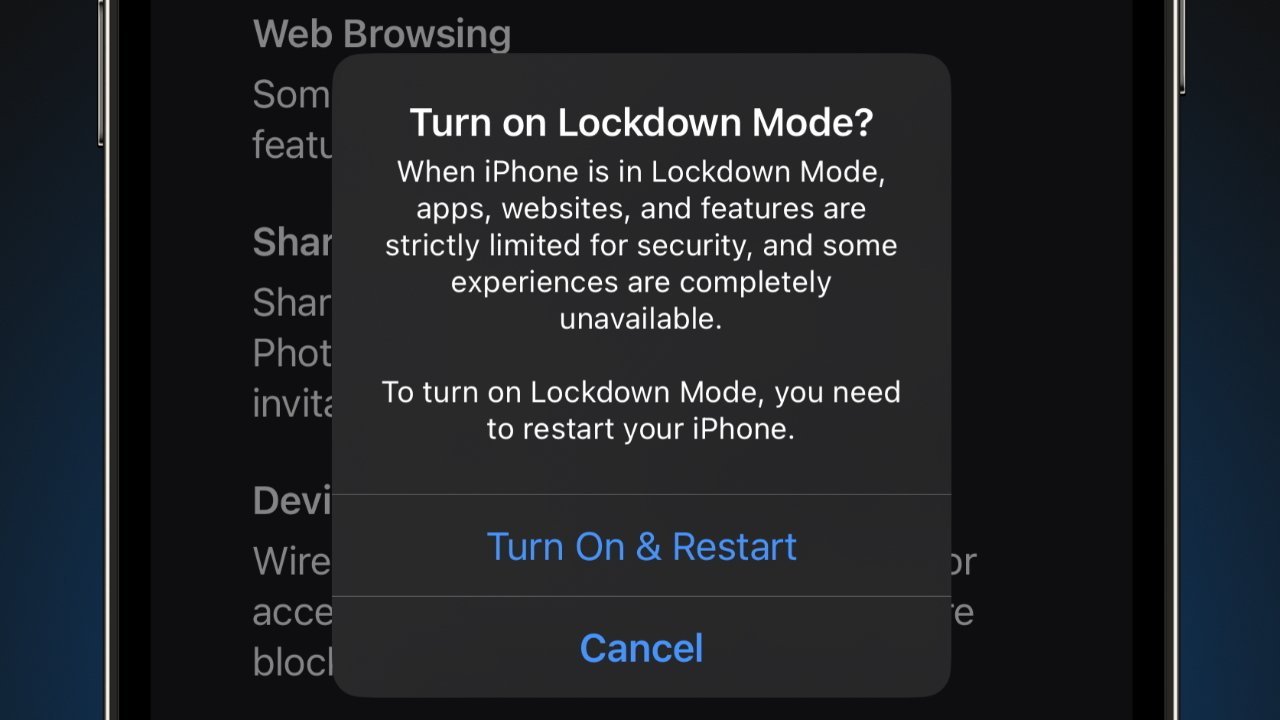
Jamf Threat Labs has worked out a proof-of-concept post-exploitation tampering technique that makes an iPhone behave appreciate it is in Lockdown Mode when it isn’t. The user can toggle Lockdown Mode and will see visual cues, appreciate an apparent device restart and warnings in Safari that trick the user into a false sense of security.
This isn’t a flaw with Lockdown Mode, iPhone security, or the operating system. The tampering technique only works on devices that have already been infected with malware.
Jamf researched this proof-of-concept to highlight that Lockdown Mode has limitations. It is a shield that reduces the attack surface on an iOS device, not anti-malware that detects infections and ejects them.
Lockdown Mode is most effective when used on a device before an attack occurs. It reduces the number of entry points available for an attacker.
A system reboot can help stop malware from monitoring the user, but Jamf found a way to force a userspace reboot instead of a system reboot. That way, the injected code can preserve adaptable control over Lockdown Mode.
Lockdown Mode performs several actions, most of which are invisible to the user.
- Messages — Most message attachments are blocked, and some features are unavailable.
- FaceTime — Incoming FaceTime calls from people you have not previously called are blocked.
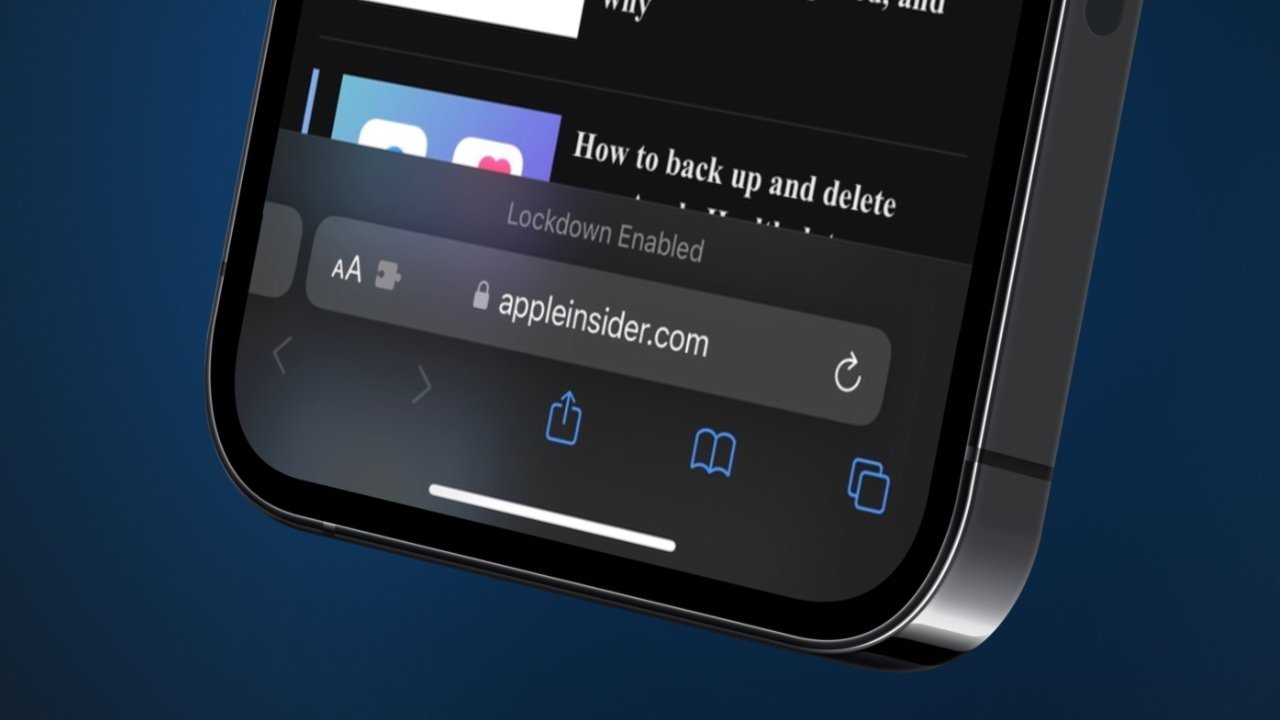
- Web Browsing — Some web technologies and browsing features are blocked.
- Shared Albums — Shared albums will be removed from the Photos app, and new Shared Albums invitations will be blocked.
- Device Connections — Wired connections with another device or accessory are blocked while your iPhone is locked.
- Apple Services — Incoming invitations for Apple Services from people you have not previously invited are blocked.
- Profiles — Configuration profiles, such as profiles for school or work, cannot be installed.
Those activating Lockdown Mode may not be familiar with everything it does, so Jamf feels that manipulating only a few points can trick users into that false sense of security. For example, they altered an alert in Safari that shows up when Lockdown Mode is active.
As was shared before, this tampering technique is only possible on an iPhone that has already been infected by malware. Sophisticated attacks appreciate these are too expensive and difficult to execute without significant resources, so regular users who aren’t diplomats or political journalists likely never need to worry about such security risks.
Apple made it clear at launch that Lockdown Mode is for specific kinds of people at high risk of attacks. Turning on the feature reduces the available feature set of an iPhone and could direct users to think their device is broken. If you need to turn it on, you’ll know.