A new malware named ‘Cuttlefish’ has been spotted infecting enterprise-grade and small office/home office (SOHO) routers to monitor data that passes through them and steal authentication information.
Lumen Technologies’ Black Lotus Labs examined the new malware and reports that Cuttlefish creates a proxy or VPN tunnel on the compromised router to exfiltrate data discreetly while bypassing security measures that detect unusual sign-ins.
The malware can also perform DNS and HTTP hijacking within private IP spaces, interfering with internal communications and possibly introducing more payloads.
Although Cuttlefish has some code that overlaps with HiatusRat, which has been previously observed in campaigns that aligned with Chinese state interests, there are no concrete links between the two, and attribution was impossible.
Black Lotus Labs says the malware has been active since at least July 2023. It is currently running an active campaign concentrated in Turkey, with a few infections elsewhere impacting satellite phone and data center services.
Cuttlefish infections
The method for the initial infection of the routers has yet to be determined, but it could involve exploiting known vulnerabilities or brute-forcing credentials.
Once access is gained to a router, a bash script (“s.sh”) is deployed and begins collecting host-based data, including details on directory listing, running processes, and active connections.
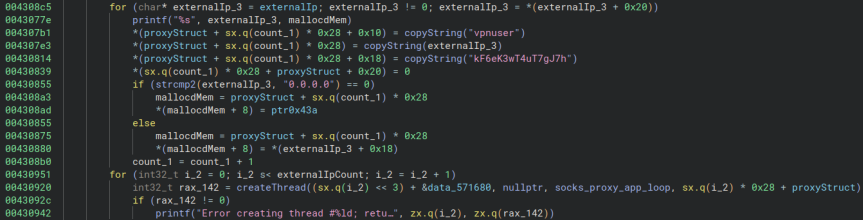
The script downloads and executes the primary Cuttlefish payload (“.timezone”), which is loaded into memory to evade detection while the downloaded file is wiped from the file system.
Black Lotus Labs reports that Cuttlefish is available in various builds supporting ARM, i386, i386_i686, i386_x64, mips32, and mips64, covering most router architectures.
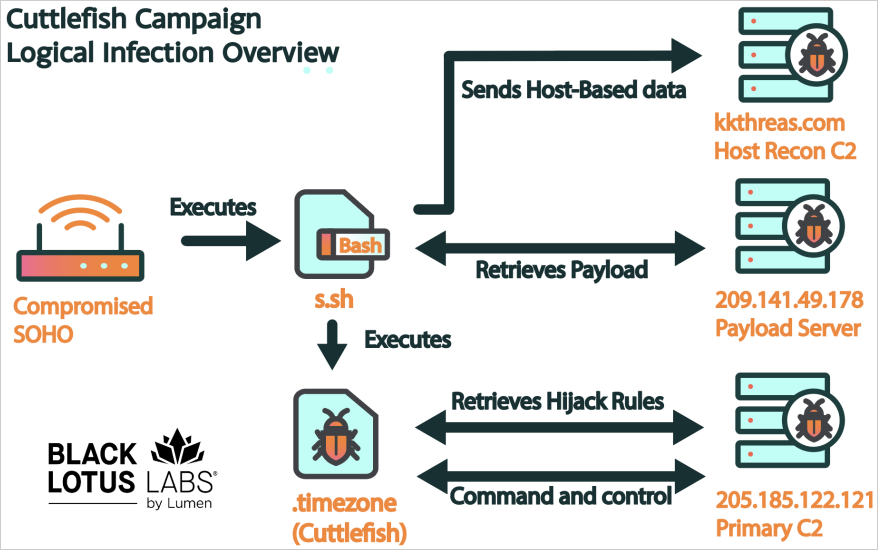
Source: Black Lotus Labs
Monitoring your traffic
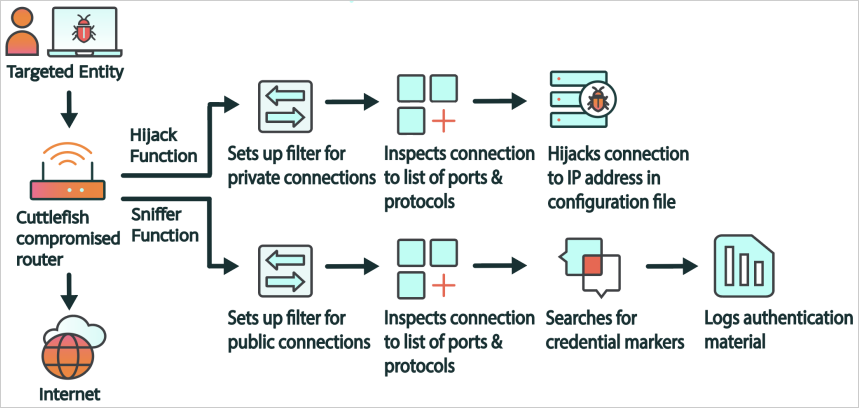
Upon execution, Cuttlefish uses a packet filter to monitor all connections through the device, and when it detects specific data, it performs a particular actions based on rulesets that are regularly updated from the attacker’s command and control (C2) server.
The malware passively sniffs packets searching for “credential markers” within the traffic, such as usernames, passwords, and tokens especially associated with public cloud-based services like Alicloud, AWS, Digital Ocean, CloudFlare, and BitBucket.
“This caught our attention as many of these services would be used to store data otherwise found within the network,” explains the Black Lotus Labs report.
“Capturing credentials in transit could allow the threat actors to copy data from cloud resourcesthat do not have the same type of logging or controls in place as traditional network perimeters.”
Data matching those parameters is logged locally, and once it reaches a certain size (1048576 bytes), it is exfiltrated to the C2 using a peer-to-peer VPN (n2n) or proxy tunnel (socks_proxy) created on the device.
Source: Black Lotus Labs
For traffic destined to private IP addresses, DNS requests are redirected to a specified DNS server, and HTTP requests are manipulated to redirect traffic to actor-controlled infrastructure using HTTP 302 error codes.
“We suspect this capability enables Cuttlefish to hijack internal (a.k.a. “east-west”) traffic through the router, or site-to-site traffic where there is a VPN connection established between routers,” explain the researchers.
“The additional function opens the door to secured resources that are not accessible via the public internet.”
Source: Black Lotus Labs
Protecting against Cuttlefish
Cuttlefish is a serious threat to organizations worldwide as it enables attackers to bypass security measures like network segmentation and endpoint monitoring and dwell undetected in cloud environments for extended periods.
Black Lotus Labs suggests that corporate network admins eliminate weak credentials, monitor for unusual logins from residential IPs, secure traffic with TLS/SSL, inspect devices for rogue iptables or other abnormal files, and routinely reboot them.
When establishing remote connections to high-value assets, it is advisable to use certificate pinning to prevent hijacking.
For SOHO router users, it is recommended to reboot the devices regularly, apply the latest available firmware updates, change default passwords, block remote access to the management interface, and replace them when they reach end-of-life (EoL).

