
Microsoft has introduced a new protective feature in the Authenticator app to block notifications that appear suspicious based on specific checks performed during the account login stage.
Microsoft Authenticator is an app that provides multi-factor authentication, password auto-fill, and password-less sign-in to Microsoft accounts.
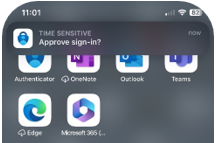
When a user tries to log into an account with protected by multi-factor authentication (MFA), the Authenticator app sends a push notification to the user’s device to grant or deny access.
(Microsoft)
Alternatively, the app generates a temporary access code for users to manually log into their account.
Hackers are known to exploit the push notification feature by performing a large number of login attempts for the target account, often at inconvenient times, hoping to frustrate or tire the recipients.
If the worn-down user approves a request, the attacker gains access to the account and may alter the login protection settings to lock the legitimate user out.
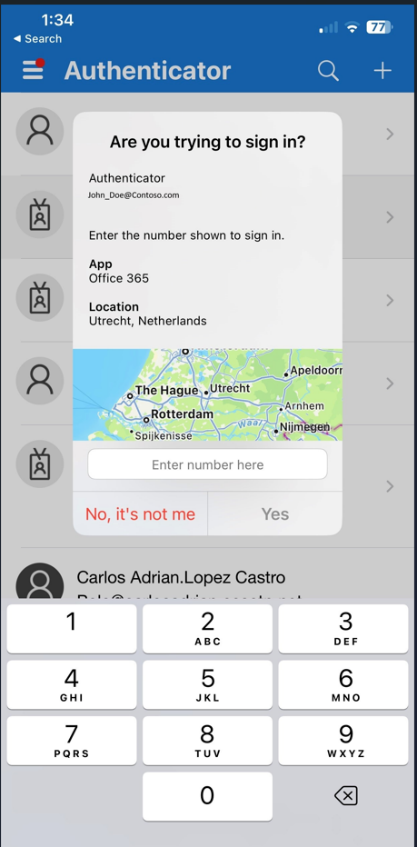
For additional security, Microsoft introduced “number matching” in May, a mechanism where the user must enter a number displayed on the sign-in screen into their Authenticator app to approve the login.
Although this measure has reduced the effectiveness of MFA fatigue attacks, it doesn’t stop the generation of the annoying notifications themselves.
To fight this malicious activity, Microsoft added new features that scrutinize details on login attempts, like if the request comes from an unfamiliar location or shows signs of anomalous activity, to blocks the notification from showing up.
Instead, users receive a message that prompts them to open the Authenticator app and enter a given code.
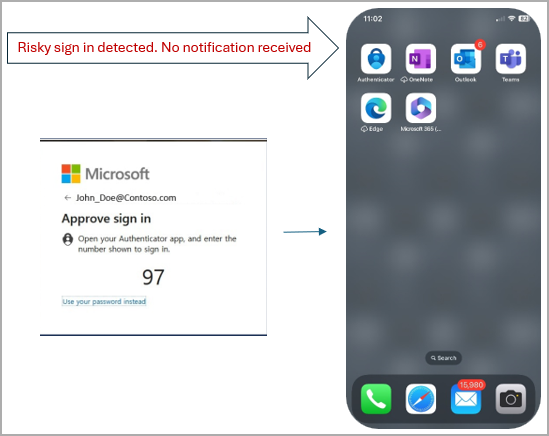
The login notifications are still generated, though, and made available from within the Authenticator App if the user needs to access and review them.
(Microsoft)
Since the roll-out of the new feature completed at the end of September, Microsoft has blocked over six million MFA notifications suspected to have been initiated by hackers.

