
Threat actors were found breaching AWS accounts using authentication secrets leaked as plaintext in Atlassian Bitbucket artifact objects.
The issue was discovered by Mandiant, who was investigating a recent exposure of Amazon Web Services (AWS) secrets that threat actors used to gain access to AWS.
Although the issue was discovered in the context of an investigation, it illustrates how data previously thought to be secured, can be leaked in plaintext to public repositories.
BitBucket’s secured variables
Bitbucket is a Git-compatible web-based version control repository and hosting service run by Atlassian, offering developers a code management and collaboration platform.
Bitbucket Pipelines is an integrated continuous delivery/deployment (CI/CD) service that automates the build, test, and deployment processes.
System admins often link Pipelines directly to AWS for rapid deployment of apps and to access resources using AWS CLI, SDKs, and other AWS tools.
To facilitate this automation, Bitbucket allows developers to store sensitive information, such as AWS authentication secrets, in ‘Secured Variables’ to easily use those variables in their code without exposing the keys to other people.
.png)
Source: Mandiant
When a variable is set as secured in BitBucket, they are stored in encrypted form to prevent public exposure of its values in the Bitbucket environment.
“You can secure a variable, which means it can be used in your scripts but its value will be hidden in the build logs (see example below),” explains the Bitbucket documentation.
“If you want to edit a secure variable, you can only give it a new value or delete it. Secure variables are stored as encrypted values.”
However, Mandiant discovered that artifact objects generated during pipeline runs can contain sensitive information, including secured variables in plaintext. As developers may not be aware that these secrets are exposed in artifact files, the source code may be published to public repositories where threat actors can steal them.
Secrets in plaintext
Artifacts are defined in the bitbucket-pipelines.yml config file used to specify a Bitbucket project’s CI/CD processes.
One of the directives in these files is artifacts:, which are used to specify variables, files, and directories that are exported to artifact objects to be retained and used in further steps of the build and testing process.
Mandiant says that it is common for developers to use the printenv command to store all environment files in a text file, which is then passed to an artifact object for future steps in the build process.
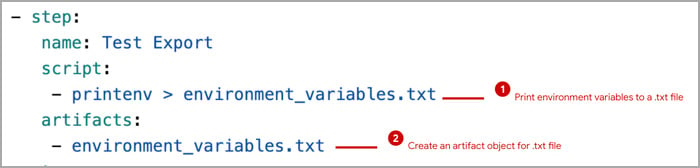
Source: Mandiant
However, doing so will cause “secured variables” to be exported in plaintext to the artifact file rather than in its encrypted form.
If those artifact files are then stored in a public location, a threat actor can simply open the text file and view all variables in plaintext, easily stealing authentication secrets that can be used to steal data or perform other malicious activity.
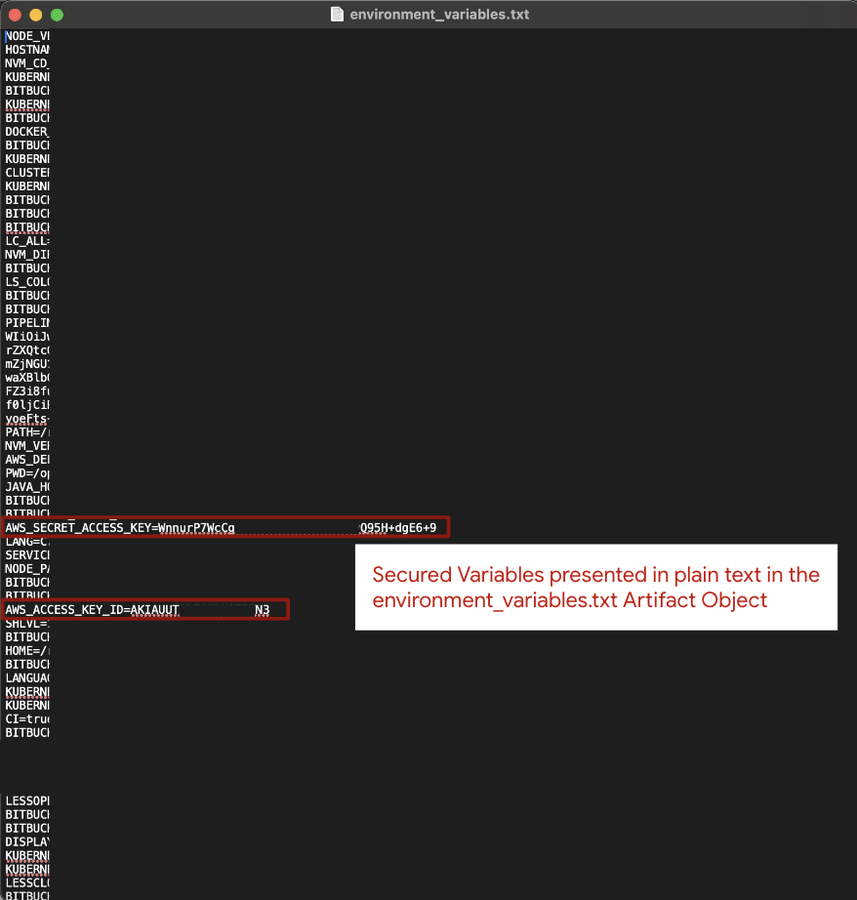
Source: Mandiant
“Mandiant has seen instances in which development teams used Bitbucket artifacts in web application source code for troubleshooting purposes, but, unbeknownst to the development teams, those artifacts contained plain text values of secret keys,” reads the report.
“This resulted in secret keys being exposed to the public internet where they were located and subsequently leveraged by attackers to gain unauthorized access.”
Another possibility according to Mandiant is misconfiguring the ‘bitbucket-pipelines.yml’ file which defines the CI/CD pipeline, to include secured variables in logs or artifacts.
When pipeline scripts log environment variables for debugging purposes, they can unintentionally log sensitive information, and since those logs are typically stored in accessible locations, there’s again a risk of secret exposure.
Mitigation tips
Mandiant reminds developers that Bitbucket was not designed to manage secrets, suggesting that a dedicated, specialized product is used for that purpose instead.
Developers are also recommended to carefully review artifacts to ensure no plain text secrets are contained inside the generated files.
Finally, it is advisable to deploy code scanning over the complete pipeline lifecycle to catch secret exposure events and remove them prior to the code reaching production.

